The internet has grown to a point where we cannot imagine life without it. From the beginning of the 21st century, we've seen an incredible growth in the number of people that have access to the internet.
Today around 40% of the world population has an internet connection, in 1995, it was less than 1%. While mankind benefits enormously from the development of networks and the internet in general, it is important to pay extra attention of the security risks that come with these developments.
Some of the latest technologies gave life to sophisticated virtual threats, making the digital world as vulnerable as it can possibly be. Therefore, it’s only normal that the biggest concern in our days is information security, commonly known as cybersecurity.

Last year, network security breaches made the headlines as never before. According to a recent Cisco report, fifty-five percent of respondents said their organisation had to deal with at least one breach in the last year.
Companies need to have full network visibility in order to stay on top of what is happening over their networks. For a better chance to prevent immediate threats (like application attacks, malware, ransomware, or exploit kits), but also to be compliant with laws like the GDPR, they need to be able to analyze actual data packets flowing through the network.
Must-Have Network Security Monitoring Tools
One of the most reliable method to monitor all the traffic is using a Network TAP. A TAP is a piece of hardware that is installed in-line on a network link. It creates an internal mirror of the traffic without disrupting it. It doesn't create any of the bottlenecks involved in using other monitoring tools (like a SPAN). TAPs guarantee full capture of 100% of packets from the live traffic in real-time because it captures packets on the wire.
Network TAPs are used extensively in security applications because they are non-intrusive and are undetectable on the network. With no physical or logical address, by using a TAP a cybersecurity team can execute their activity in complete stealth mode. Also, Network TAPs are approved as evidence in CALEA (The Commission on Accreditation for Law Enforcement Agencies, Inc.) and Lawful Intercept cases.
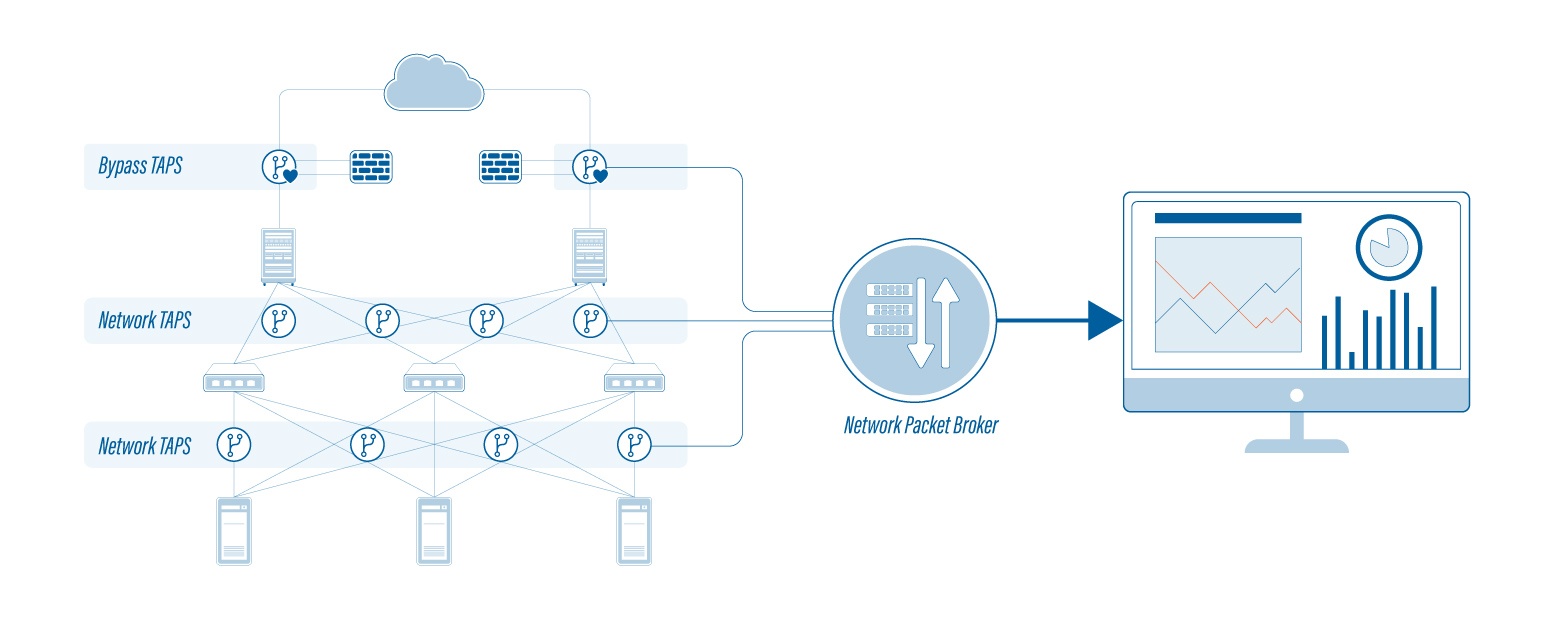
 When dealing with a high-speed data center network that's constantly evolving, your cybersecurity team needs a next-level visibility platform. High-density NPBs and Bypass TAPs are intelligent devices that complement your data center network TAPs for in-depth monitoring.
When dealing with a high-speed data center network that's constantly evolving, your cybersecurity team needs a next-level visibility platform. High-density NPBs and Bypass TAPs are intelligent devices that complement your data center network TAPs for in-depth monitoring.
An NPB's main function is to filter specific network traffic (coming through the network TAP) to a specific monitoring tool, in order to optimize security and traffic flow. Therefore, a Network Packet Broker provides actionable data to your in-line security appliances, so that they are able to make a complete and accurate analysis. Read more in this article about NPBs.
Bypass TAPs, on the other hand, are valuable devices that support active in-line network security and performance tools. Active in-line security tools are single points of failure in any network. They can fail at any time, either due to a hardware malfunction, power loss, or software problem. That's where the Bypass TAP comes in handy, because it keeps the link flowing, while a redundant path can be activated. This way it can always keep the critical link up until the issue is fixed.
There can also be situations where cybersecurity teams need a tool while on the field. Among the fastest and portable packet capture devices in the world, our ProfiShark series are the perfect tools for field troubleshooting. They are similar to aggregation TAPs, but without the bottlenecks of packet drops or time delay. With two Gigabit network ports, they seamlessly combine the two traffic streams into a single monitoring port. More about our ProfiShark series on our website.
An Unpredictable Future
There is no way of knowing how cyberthreats will evolve or the ways they can hit your network. All we can be sure of is that having greater visibility and analysis into your data will give your cybersecurity teams more chances to stop cyber crimes from happening.
The first and most important step to having a successful cybersecurity strategy is, as we said above, understanding the need for network packet capture devices and build your analytics platform out from there. These tools give your team the chance to counter and neutralize threats in real-time by capturing and analyzing live traffic packets.

