In today's modern network architecture, monitoring and security tools are required to handle traffic coming from multiple visibility devices including network TAPs or SPAN port. Each of these tools possess a different requirement. In addition, the volume and diversity of traffic can also be overwhelming to these tools. Network Packet Brokers (NPBs) are able to address this challenge by providing a more centralized and intelligent way to manage data forwarding to the monitoring tools.
To do all this, however, NPBs must be capable of managing the relentless growth in network traffic, the multiplication and constant evolution of monitoring and security appliances also the increasing complexity brought by virtualization technologies.

Introducing Next-Generation Network Packet Brokers (NGNPBs)
To accommodate the needs of digital businesses, NPBs capabilities have evolved. Aside from its core functionality such as intelligent aggregation, advanced filtering and load balancing, the NGNPBs offer the following extensive set of features:
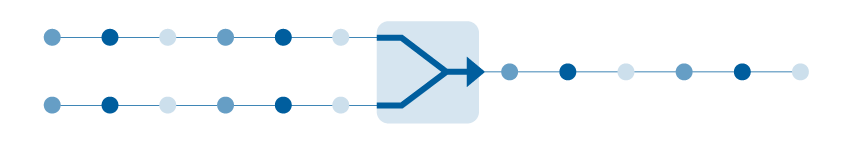
Packet Slicing
Packet slicing is one of the most important features that NGNPBs have. Networks and servers only have a limited amount of data storage. If your network can't cope with the amount of traffic, then packets are more likely to get lost. To prevent this from happening, you need to make sure your device isn't being wasted on maintaining unnecessary packet payload. How? By removing payload that is irrelevant to your network monitoring and security analysis. When the payload is reduced, the system can run more efficiently.
When using packet slicing, the filter slices a packet to the size of the frame through the header. If you remove payload data from packets and leave only the header information, you ensure that only the right data is captured and sent across to the appropriate tool. As a result, the performance of your tools will be improved as the throughput and storage space are reduced. another benefit of this feature is in security compliance. With packet slicing, you will be able to take out confidential data before it reaches your monitoring tools. This to ensure that this sensitive data is not being stored outside secure boundaries.
 Figure 1. Packet Slicing
Figure 1. Packet Slicing
GTP IP Filtering
According to Statista, mobile accounts for approximately half of web traffic worldwide and is projected to grow substantially in total of traffic volumes. Most traffic generated will be real-time video and multimedia files requiring increased bandwidth and fast connection. As this demand will continue to explode, mobile wireless networks must expand greatly in capacities.
GTP is a group of IP-based communications protocols used to carry GPRS traffic within GSM and UTMS networks. It is designed as a carrier to transport actual mobile packets over the network via tunneling. The tunnel is a channel between multiple GPRS support nodes through which the hosts exchange data. All IP addresses in the GTP packets are for mobile network elements such as the base station and the serving gateway.
When IP tunneling is used to deliver IP traffic across the core network using GTP, there can be multiple layers of encapsulation and addressing within the IP traffic. That's where GTP IP filtering feature comes handy. This feature will allow you to filter by IP in GTP sessions based on information in the data stream to control data flows within your infrastructure. This can be done by configuring the device to pass or drop the encapsulated traffic that doesn't match the packet policy from mobile station through identifying the source and the destination.
Figure 2. GTP IP Filtering
ERSPAN Tunneling & De-Tunneling
(GRE tunneling and de-tunneling, VXLAN de-tunneling, and ERSPAN stripping)
Beyond scalable aggregation, replication, NGNPBs provides access to traffic through a variety of complex tunneling protocols such as, Encapsulated Remote SPAN (ERSPAN), Generic Routing Encapsulation (GRE), Virtual Extensible LAN (VXLAN). These advanced tunneling features will help you to ease blind spot of multiple traffic traversing on network anywhere within your IT infrastructure whether it is locally or remotely, physically or virtually.
Track packets easily by adding IDs to packets based on the source (ingress) port and remove them as they leave the NGNPBs via exit (egress) ports. Using this approach, packets are encapsulated and directed from a switch/VLAN to a target IP endpoint with GRE or ERSPAN tunneling and send to the appropriate tools. Also, by identifying and stripping the protocol, Network Engineers can selectively dictate which types of traffic should be routed to a specific device for further analysis.
 Figure 3. ERSPAN Tunneling & De-Tunneling
Figure 3. ERSPAN Tunneling & De-Tunneling
Packet Deduplication
Duplicate packets are very common in networks and unavoidable, especially when you are using SPAN/mirror port. When duplicate packets are transmitted to your monitoring tools, the tools can be overloaded resulting in inefficiency. For that reason, eliminating identical packets is crucial. Not only will this improve the data capacity but also enhance your network performance to achieve your monitoring goals.
Network Packet Broker can eliminate duplicate packets before forwarding the traffic to the monitoring tools. With this packet deduplication technology, similar copies will be dropped from the data stream to reduce overhead. When your network monitoring tools don't have to deal with problems associated with duplicate packets, they can store and process as much useful data without the unwanted duplicates being transmitted to them. This will increase the visibility across your network and allow your tools to accurately perform its tasks.
Figure 4. Packet Deduplication
The effectiveness of your appliances can be compromised by the explosive growth of network traffic and the complexity of technologies. These advanced capabilities of NGNPBs are critical to the success of your organization. But NGNPBs are not all made with equivalent capabilities. You will need to find one that performs all functions required for your network architecture today and in the future. Interested to learn how to optimize the Network Packet Brokers efficiency? Then read this article.