Most of the times, when your network crashes or you come across an issue, you have to search through your captured packets to find the problem. This is where a tool like Wireshark comes in handy. One of the most used network protocol analyzer out there, it analyzes the files that come out of your network TAP (called also a packet capture device) or your computer’s NIC and lets you have an in-depth look into their parameters, messages, format, etc.
Unfortunately, the amount of information you will get when capturing a network line can be daunting. Capturing so many packets, means that you will end up seeing huge captured files. Thankfully, Wireshark allows the user to quickly filter all that data, so you only see the parts you’re interested in, like a certain IP source or destination. You can even compare values, search for strings, hide unnecessary protocols and so on.
Most of the following display filters work on live capture, as well as for imported files, giving you the possibility to filter on almost any field of any protocol, down to the HEX values of your data streams. What you want to filter on exactly depends on your specific situation and purpose, of course.
We’ve asked our engineers what are their favourite filters and how they use them. The following are their preferred choices.
ip.addr == x.x.x.x
ip.addr == x.x.x.x && ip.addr == x.x.x.x
(or ip.src == xxxx && ip.dst == xxxx - for a destination)
Sets a conversation filter between two specific IP addresses. This one helps you check the data between two specific hosts or networks. It helps you when you are looking for specific data, so you don’t have to go through others that don’t interest you.
http or dns
Sets a filter to display all http and dns protocols. It lets you narrow down to the exact protocol you need. So, if you need to track down an odd FTP traffic, then you just have to set it for ‘ftp’. Want to find out why some websites don’t appear? You just have to set it to ‘dns’.
tcp.port==xxx
Sets filters for any TCP packet with a specific source or destination port. Sometimes is just useful and less time consuming to look only at the traffic that goes into or out of a specific port.
tcp.flags.reset==1
Sets filters to display all TCP resets. All packets have a TCP, if this is set to 1, it tells the receiving computer that it should at once stop using that connection. So, this filter is a powerful one, being that a TCP reset kills a TCP connection immediately.
tcp contains xxx
It’s a filter that displays all TCP packets that contain a certain term (instead of xxx, use what term you’re looking for). For example, if you are looking for a specific term appearing in the packet, this filter is what you need.
tcp.stream eq X
Follows a tcp stream.
tcp.seq == x
Filters by sequence number.
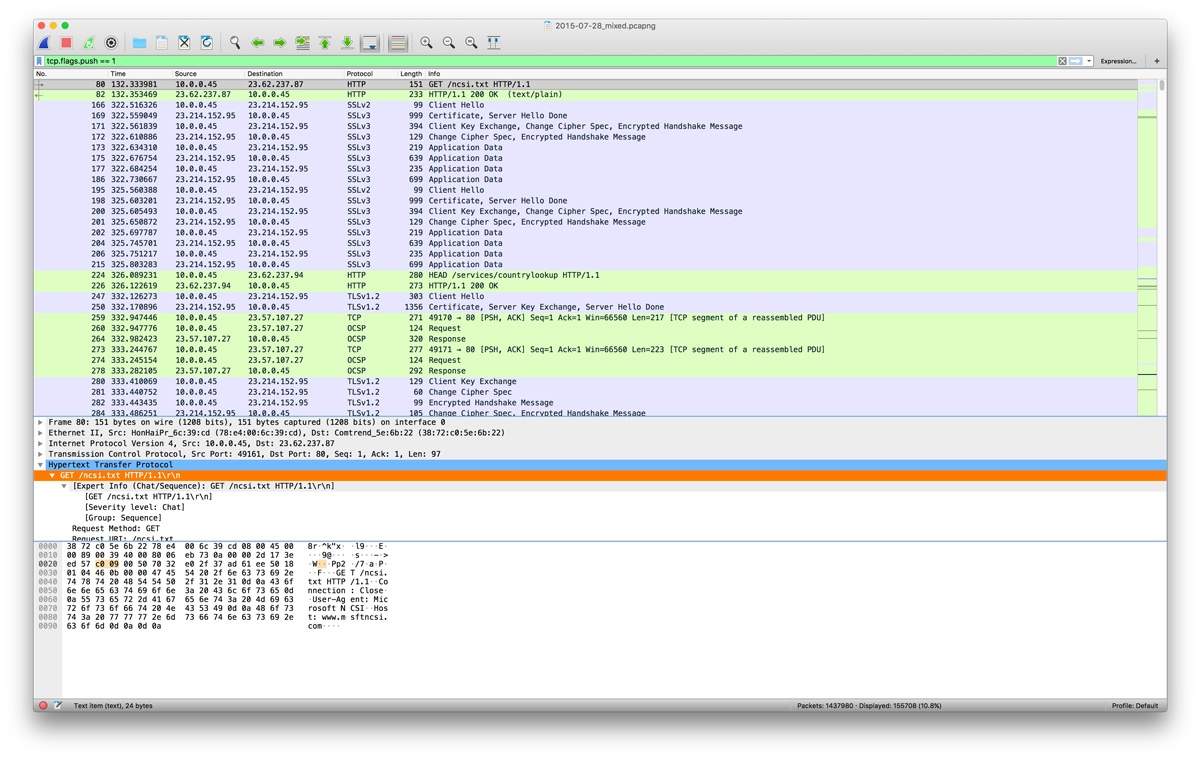
tcp.flags.push == 1
Important for troubleshooting, this filter detects push events.
http.request
This one filters all HTTP GET and POST requests. It can show the most accessed webpages.
!(arp or icmp or dns)
Designed to filter out certain types of protocols, it masks out arp, icmp, dns, or other protocols you think are not useful. This will allow you to focus of what traffic interests you.
udp contains xx:xx:xx
It sets a filter for certain HEX values at any offset.
dns.flags.rcode != 0
Indicates which dns requests couldn't be correctly resolved.
Don't forget to check The Evolution of Portable Packet Capture Solutions article if you want to learn more about a portable network capture solution that flawlessly integrates with Wireshark.